How To Protect Yourself From Data Breaches


Data breaches are a growing concern in our digital world. They can expose sensitive information and lead to severe consequences. Understanding how to protect yourself is crucial.
A data breach occurs when unauthorized individuals access confidential data. This can happen through various means, such as weak passwords or phishing attacks. The impact can be devastating, affecting both individuals and businesses.
Preventing data breaches requires vigilance and proactive measures. Simple steps like using strong passwords and enabling two-factor authentication can make a difference. Companies must also implement robust security protocols to safeguard their data.
In this guide, we will explore how data breaches happen and how you can protect yourself. Stay informed and secure your digital life.
What Is a Data Breach? Definitions and Key Concepts
A data breach is an incident where sensitive information is accessed without authorization. This can involve personal data, financial records, or proprietary company information. Understanding key concepts of data breaches helps in grasping their potential impact.
The privacy breach definition relates to unauthorized access to personal data. Breaches can result from various incidents, including hacking, insider threats, or accidental data exposures. A breach of the Data Protection Act can lead to legal actions against the responsible entity.
When considering breaches, it’s essential to know:
- Data breach definition: Unauthorized access or retrieval of data.
- Cyber breach definition: Breach involving digital data and networks.
- Security leak: Information unintendedly disclosed.
Understanding these terms assists in identifying the scope and severity of a breach incident. Knowing these concepts can guide individuals and companies in effectively managing and mitigating breaches.
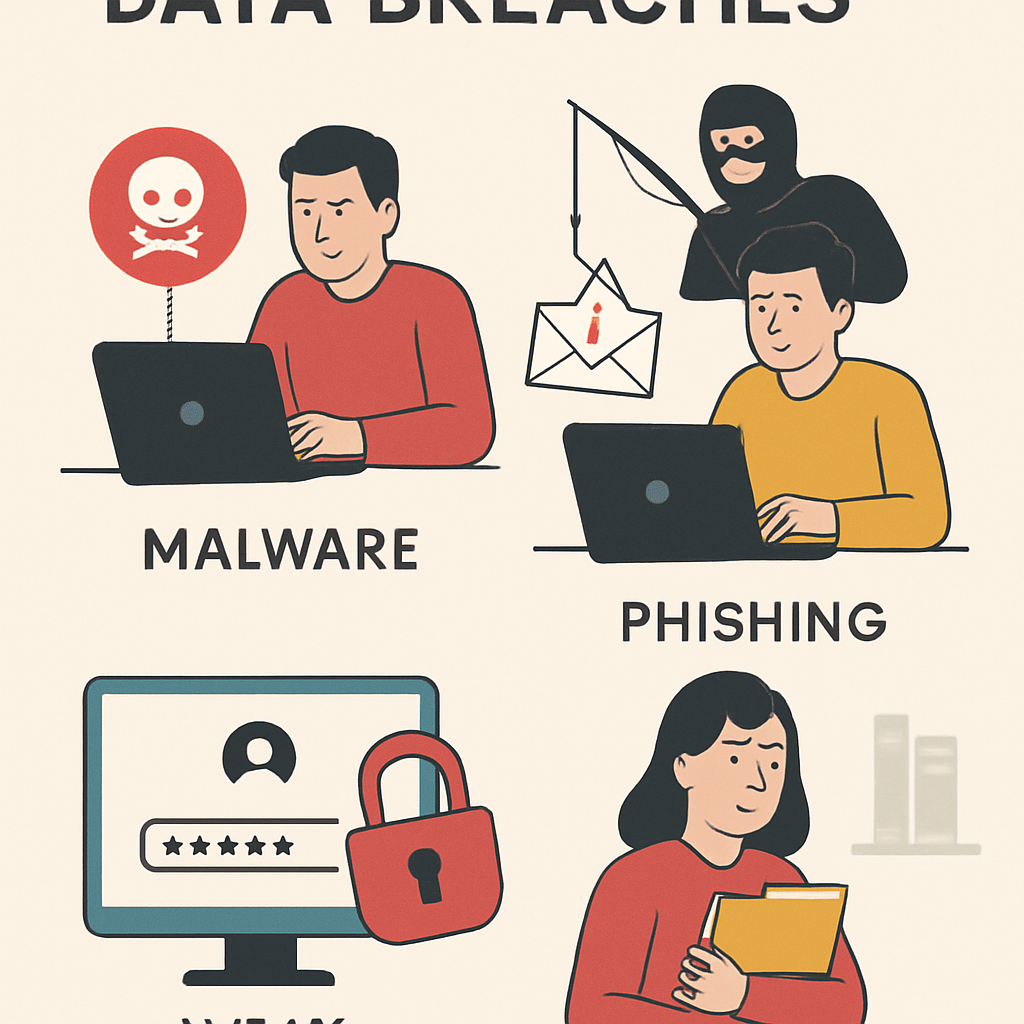
How Do Data Breaches Happen? Common Causes and Examples
Data breaches often stem from several causes, each with significant implications. Weak passwords are a frequent culprit, making it easy for attackers to access accounts. Phishing attacks deceive individuals into sharing sensitive information, such as passwords or credit card numbers.
Companies are not immune to breaches caused by their systems. Unpatched software vulnerabilities create pathways for cybercriminals. These security leaks can be exploited quickly, resulting in unauthorized data access. Malware infections compromise systems and allow data to be stolen without user knowledge.
Here are some common causes of data breaches:
- Weak passwords: Easily guessed or reused passwords.
- Phishing attacks: Deceptive communications tricking individuals.
- Malware: Malicious software gaining unauthorized access.
- Unpatched software: Neglected updates leading to vulnerabilities.
An example of a database breach is when customer credit card information is stolen from a retailer’s database. This can lead to massive financial losses and identity theft for affected customers. Understanding how data breaches happen is crucial for both preventing and responding to them.
The Impact of Data Breaches: Why Prevention Matters
The impact of a data breach can be devastating. Compromised personal information often leads to identity theft. Victims may suffer financial losses and emotional distress, which can take years to resolve.
Businesses face dire consequences from data breaches. They can experience severe reputational damage, leading to a loss of customer trust. Legal repercussions and regulatory fines can add to their woes. The cost of a data breach can be overwhelming, affecting both small and large companies.
Preventing data breaches should be a top priority. The consequences for individuals and businesses highlight the importance of stringent security measures. Here are some critical reasons why prevention matters:
- Identity theft risk: Protecting personal information is crucial.
- Financial implications: Data breaches are expensive to address.
- Reputational harm: Maintaining customer trust is vital.
- Legal compliance: Avoid penalties and fines by safeguarding data.
How to Prevent Data Breaches: Best Practices for Individuals
Protecting your personal data is essential in today’s digital age. Individuals should adopt best practices to safeguard their information from breaches. Simple steps can make a significant difference in preventing unauthorized access.
Start by securing your passwords. Use a mix of letters, numbers, and symbols. Avoid using the same password across different accounts. Changing passwords regularly can also add a layer of security.
Consider enabling multi-factor authentication wherever possible. This adds an extra barrier for anyone trying to access your accounts. It’s an effective way to prevent unauthorized entry, even if your password is compromised.
Being vigilant about email and online interactions is also crucial. Phishing attacks are a common method hackers use to gain access. Be skeptical of emails asking for personal information or directing you to unfamiliar websites.
Keep your software and apps updated. Updates often include security patches that fix vulnerabilities. Regular updates help protect your devices from cyber threats.
Be cautious with public Wi-Fi networks. They are often unsecured and can be a hotspot for data theft. If you must use public Wi-Fi, consider using a VPN to encrypt your data.
Key Measures:
- Secure passwords: Use complex and unique passwords.
- Enable multi-factor authentication: Enhance account security.
Additional Tips:
- Be aware of phishing scams: Don’t click on suspicious links.
- Keep software updated: Install updates regularly.

By following these best practices, individuals can take proactive steps to protect their personal data and reduce the risk of breaches.
How to Prevent Data Breaches: Best Practices for Companies
Companies are key targets for data breaches due to the vast amounts of valuable information they handle. To protect against data breaches, businesses must implement strong cybersecurity measures. Here’s how companies can safeguard their data.
Start by conducting regular security audits. These audits help identify vulnerabilities in your systems. Addressing these weaknesses promptly can significantly reduce the risk of breaches.
Educate employees about data security. They should recognize phishing attempts and report suspicious activities. Regular training sessions can keep security practices top-of-mind for your staff.
Implement strict access controls. Only grant data access to personnel who need it for their roles. Limiting access minimizes the potential for unauthorized data entry.
Encrypt sensitive data both in transit and at rest. Encryption transforms data into unreadable formats for unauthorized users. This adds an essential layer of security in case of breaches.
Monitor and analyze network traffic. This helps detect unusual activities that could signal a breach. Acting quickly upon detecting these anomalies can prevent data loss.
Essential Steps for Companies:
- Conduct security audits: Regularly check for system vulnerabilities.
- Educate employees: Train staff on recognizing security threats.
Critical Practices:
- Implement access controls: Limit who can view or edit data.
- Use encryption: Protect sensitive information with encryption methods.

By adopting these practices, companies can strengthen their defenses against data breaches and protect their valuable information.
Data Breach Mitigation: What to Do If You’re Affected
Discovering that you are part of a data breach can be alarming. Swift action is essential to mitigate potential damage. First, determine the scope of the breach and what information was compromised.
Contact your bank and other financial institutions immediately if sensitive financial information is involved. They can monitor your accounts for suspicious activity and prevent unauthorized transactions. It may also be necessary to change your banking passwords.
Consider placing a fraud alert on your credit report. This informs lenders to take extra precautions before opening new accounts in your name, reducing the risk of identity theft.
Be proactive in monitoring your accounts and credit report. Catching anomalies early can prevent further issues. Also, update your passwords for any affected accounts and enable multifactor authentication where possible.
Quick Actions to Take:
- Notify financial institutions: Protect your financial information immediately.
- Set a fraud alert: Reduce identity theft risks.
Ongoing Measures:
- Monitor accounts: Keep an eye on your financial transactions.
- Change passwords: Ensure your account security is updated.
These steps can help contain the breach’s effects and safeguard your personal information.
Legal and Regulatory Considerations: Data Protection Laws and Compliance
Understanding data protection laws is crucial for anyone handling personal information. These laws, like the GDPR or the Data Protection Act, outline how organizations should manage and protect user data. Non-compliance can result in significant fines and damage to reputation.
Compliance involves regular audits and employee training. Organizations must stay informed about changes in legislation to avoid legal pitfalls. Ensuring compliance not only prevents legal issues but also builds trust with customers.
Key Data Protection Principles:
- Transparency: Inform users about data collection and usage.
- Security: Implement measures to protect data from breaches.
- Accountability: Be responsible for data protection practices.
Following these guidelines helps in maintaining robust data governance. Proper adherence to laws and regulations ensures that sensitive information remains secure, fostering trust and confidence among stakeholders.
Building a Data Breach Response Plan
A well-prepared response plan is essential for mitigating the impact of a data breach. This plan outlines steps to take immediately following a breach to minimize damage. Effective response can protect your reputation and limit financial loss.
Key components of a data breach response plan include:
- Detection and Analysis: Identify the breach and assess its scope.
- Containment: Prevent further unauthorized data access.
- Eradication and Recovery: Remove threats and restore systems.
- Communication: Notify affected parties and stakeholders.
- Evaluation: Review and improve response strategies.
Regularly test your plan to ensure its effectiveness. By being proactive, you can respond to breaches swiftly and efficiently, reducing their overall impact.
Frequently Asked Questions About Data Breaches
Understanding data breaches can be complex. Here are some common questions that might help clarify things. These FAQs cover the basics, providing quick and clear insights into essential aspects.
- What is a data breach?
- How does a data breach happen?
- What should you do if your data is breached?
- How can companies prevent data breaches?
- What are the legal implications of a data breach?
These questions address the fundamentals of data breaches. They offer a starting point for those wanting to learn more or take preventive steps. Always stay informed to protect your data effectively.
Conclusion: Staying Vigilant Against Data Breaches
Data breaches pose a serious threat to both individuals and businesses. By staying vigilant and practicing robust security measures, you can significantly reduce the risk of unauthorized access to your data. Implementing these measures requires ongoing attention and effort.
Awareness and education are key components in the fight against data breaches. Regular updates on new threats and security strategies help maintain strong defenses. Ensure you and your organization prioritize data protection to safeguard against the ever-evolving landscape of cyber threats. Remember, effective prevention is a continuous process, demanding constant care.